CVE-2023-33293: Verify Installed App Version on KaiOS 3.0 & 3.1
Vendor: KaiOS Technologies Inc.
Vendor URL: https://www.kaiostech.com/
Versions affected: KaiOS 3.0, KaiOS 3.1
Systems Affected: KaiOS-based mobile devices
Author: Tom Barrasso
CVE Identifier: CVE-2023-33293
Risk: Low
Summary
KaiOS is a mobile operating system based on Firefox OS. The operating system comes with the api-daemon binary exposing a local web server that responds to HTTP requests on port 80 under the hostname localhost.
This server also exposes subdomains for each installed applications, http://myapp.localhost, as well as reserved hostnames cached.localhost for cached Progressive Web Apps (PWAs) and shared.localhost for a bundle of shared system resources. These can be used to fetch assets that are part of the application's bundle.
Location
- Source:
/system/kaios/api-daemon
Impact
An attacker can make fetch requests to determine if a given app is installed. Given that KaiOS 3.0 has about ~400 apps available, it's easily feasible to replicate the process to return all installed apps.
Exposing whether the user has a given app installed can be used for digital fingerprinting as well as targeted phishing. Additionally, because the manifest is returned in the HTTP response with proper CORS headers, it is also possible to extract additional information such as the app version.
Recommendation
api-daemon should check the Origin header and only return valid responses for the same application, or to shared.localhost. These checks could be further extended to encompass Digital Asset Links validation used by Android and iOS to allow a website to check if related apps are installed.
This approach is more robust but would allow websites, not just apps, to check if their corresponding app is installed.
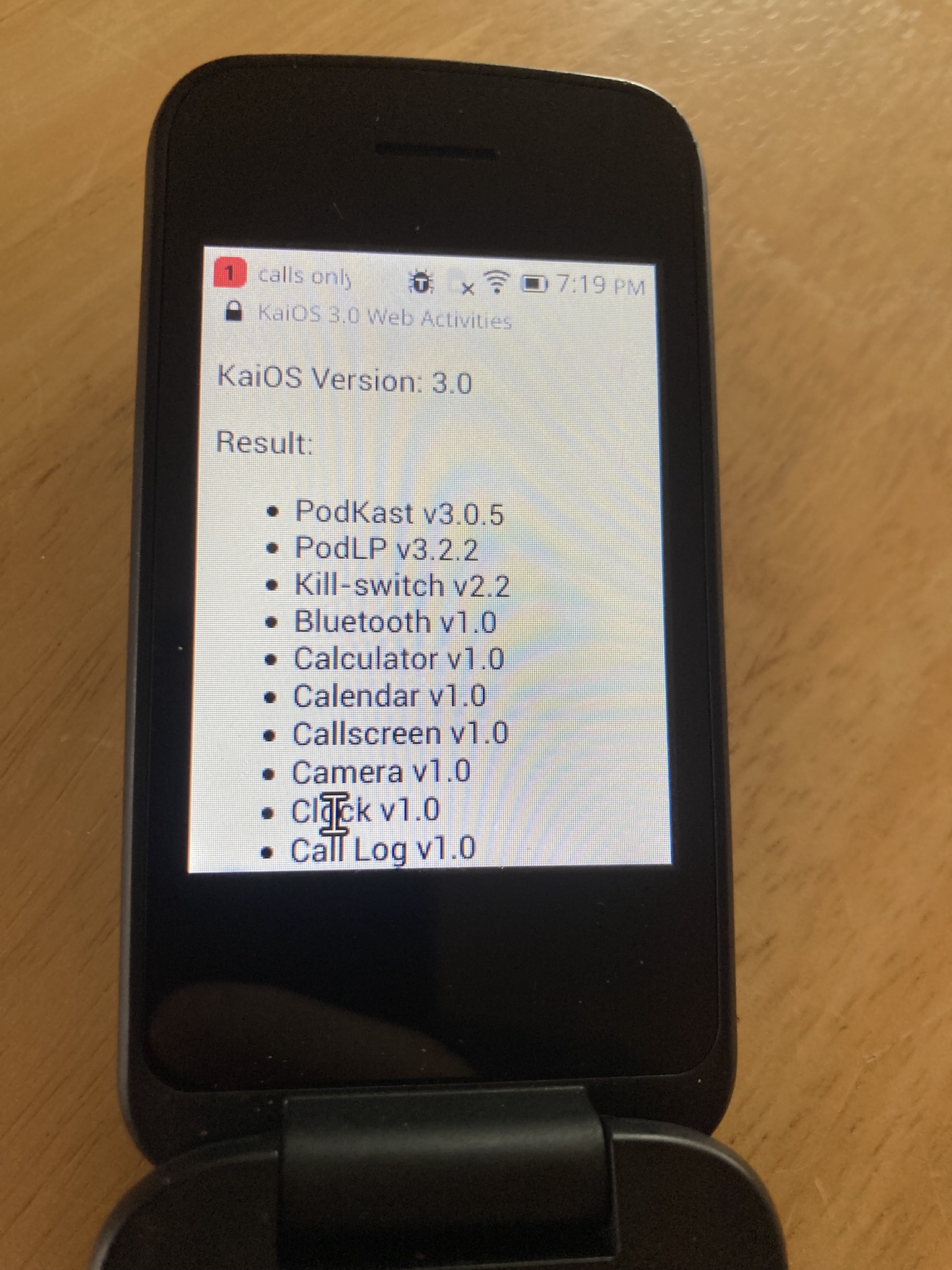
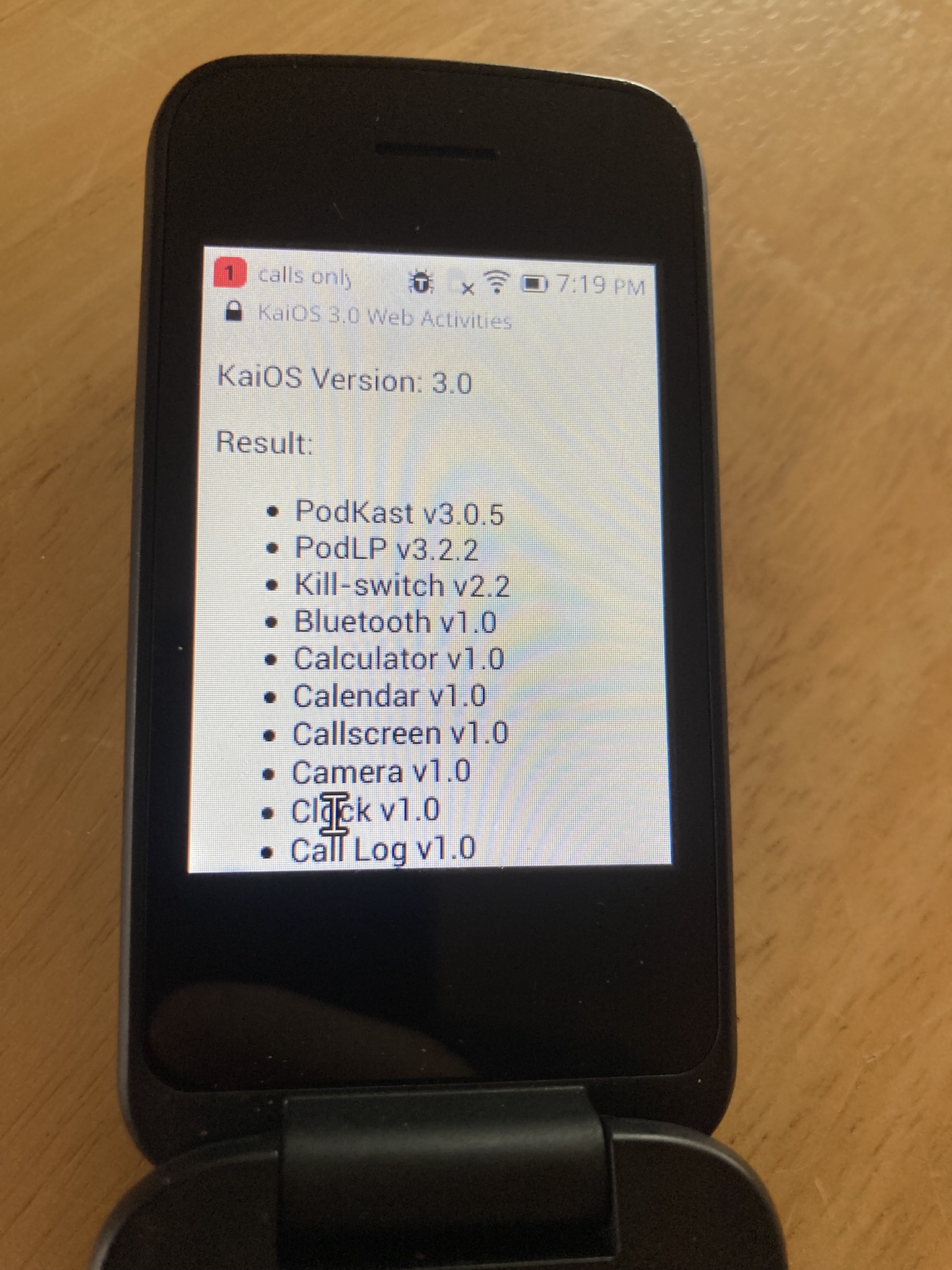
Demo
This demo lists all installed applications and their installed version. It does not check installed PWAs, but could be adapted to check http://cached.localhost/myapp/.
Vendor Communication Timeline
- 5/2/23: Tom emailed [email protected] asking for PGP key used for secure communication.
- 5/5/23: Tom disclosed issues to KaiOS Technologies.
- 5/8/23: KaiOS Technologies acknowledged this issue.
- 5/15/23: Tom asked for the current remediation status.